As per what I mentioned in the past about Computer
Forensic is mainly about story telling by presenting the fact to facilitate the
investigating works and the judgement of the case, reporting would be one of
the most critical area that demonstrating the examiners seniority following the
analysis skill level. Computer forensic
report is usually litigious and likely to be distributed to both technologies
technical and non-technical parties. As
such, accurately presenting the fact in a human-readable way with no bias would
always be the key of writing a good report and, going forward, the following
would be some noticeable requirements and pre-concept according to my computer
forensic examiner’s experience.
1. Reporting purpose
The ultimate objective of reporting is to present
the fact to address the technical concern.
This must be presented in the manner of understandable and
human-readable. Jargon must be carefully
identified assuming that the readers are having zero computer knowledge
especially if the report is going to be used in litigations, the report readers
would then likely to be non-technical individuals, such as attorneys, judge,
jury, etc. Besides, since the report may
be the only opportunity to present the facts found in the investigation, this
must encompass the whole of any testimony in details for the trier of fact.
Otherwise this may induce serious financial and legal consequences due to misrepresent
any of the findings.
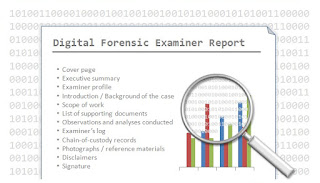
2. Report structure and style
Ideally all examiner reports are required to be
capable in standing on their own and providing the clear and accurate
information to anyone, who read the report, to reach the same conclusions. Terms such as “many”, “significantly”, highly”,
etc, which are subjective and able to be interpreted in multiple ways must be
avoided. Industrial accepted reference
should be used whenever possible as to substantiate the statements and the
content presented. Also, every single
page should contain a unique identifier include the report title, date of issue
and also the examiner basic info / company name for references purpose. The more importantly, the examiner’s
background are suggested to be clear state and identified at the beginning of
the report and the following are the sections that typically included in the
examiner reports:-
·
Cover page
·
Executive summary
·
Examiner profile
·
Introduction / Background of the case
·
Scope of work
·
List of supporting documents
·
Observations and analyses conducted
·
Examiner’s log
·
Chain-of-custody records
·
Photographs / reference materials
·
Disclaimers
·
Signature
3. Quality assurance
When the issues are complex, mistake and errors may
always be present no matter how careful the examiner is. As such, peer review for me would be
suggested as one of the most effective and essential way to resolve these
issues. Peer review is to conduct by the
one who is at the same level or more senior than you in terms of
experience. At least two peers are
suggested for you to invite as your peer reviewer. It is not only a general review in terms of
grammatical errors or the phases and wordings used, but also a quality
assurance on any of the assumptions and analysis made under the report.
Previous Step